1983: Three Inventors Receive Patent for Encryption Algorithm RSA : Cryptologic Dates in History Calendar
Understanding RSA Encryption: The Rivest-Shamir-Adleman Algorithm | by Karthikeyan Nagaraj | InfoSec Write-ups

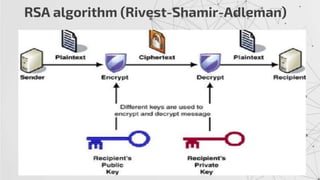
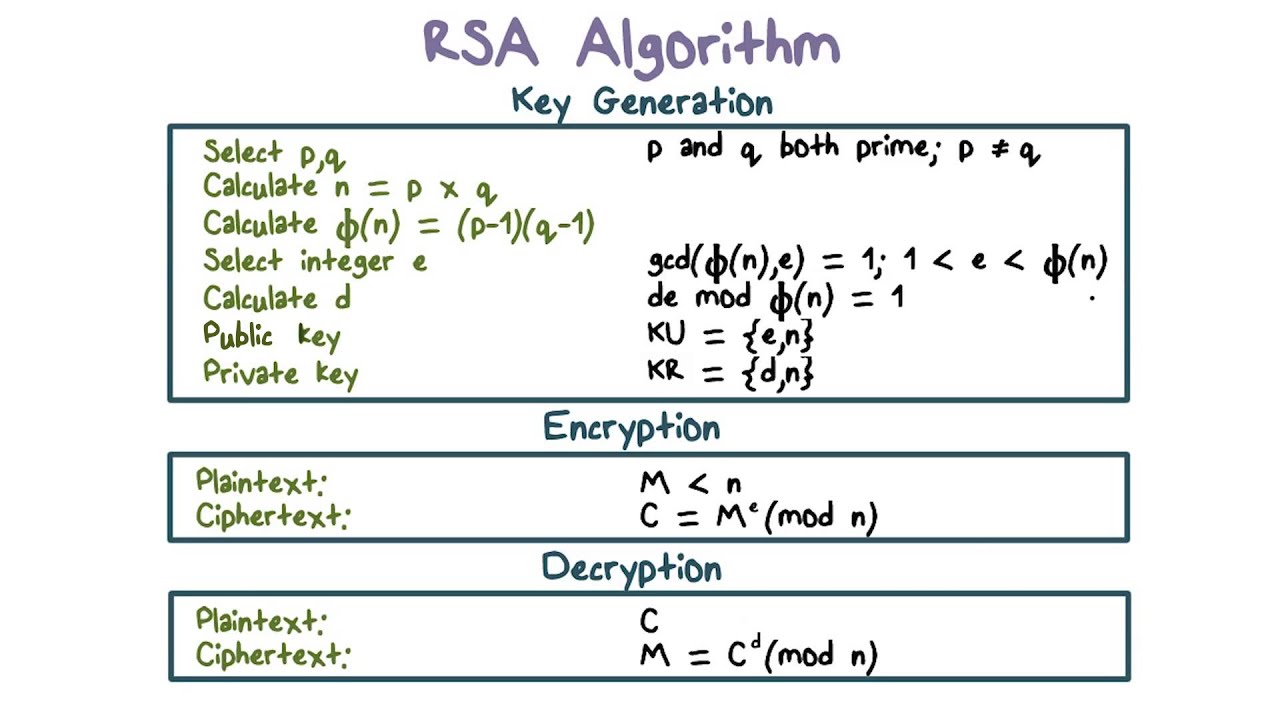
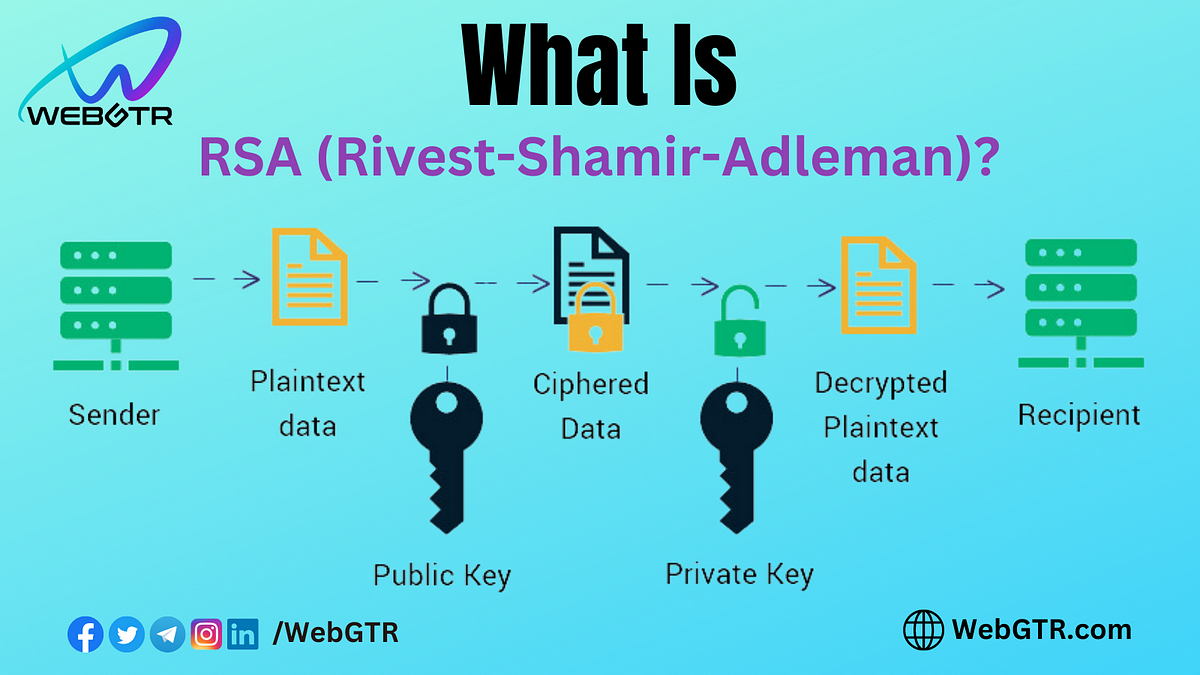
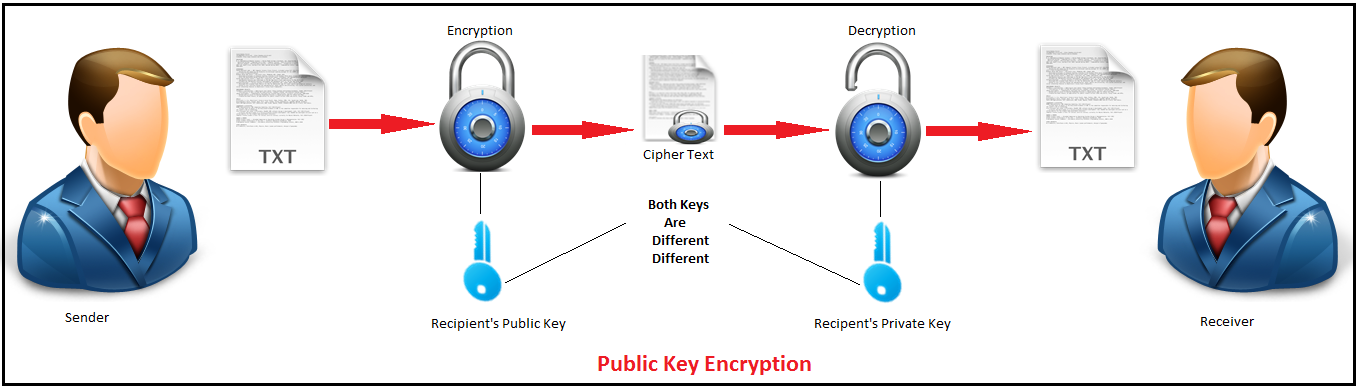
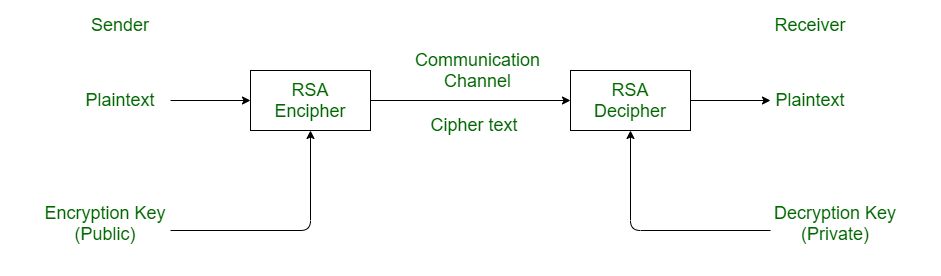
GitHub - AbdullahAlhussein/RSA-Algorithm: RSA (Rivest–Shamir–Adleman) is an algorithm used by modern computers to encrypt and decrypt messages. It is an asymmetric cryptographic algorithm. Asymmetric means that there are two different keys. This
Combination of Farnet and Rivest-Shamir-Adleman (RSA) to encrypt the... | Download Scientific Diagram

criptosistema rivest shamir adleman. crittografia e sicurezza della rete. rsa 5170900 Stock Photo su Vecteezy

RSA. Rivest Shamir Adleman del sistema crittografico. La crittografia e la protezione della rete Foto stock - Alamy

RSA. Rivest Shamir Adleman del sistema crittografico. La crittografia e la protezione della rete Foto stock - Alamy
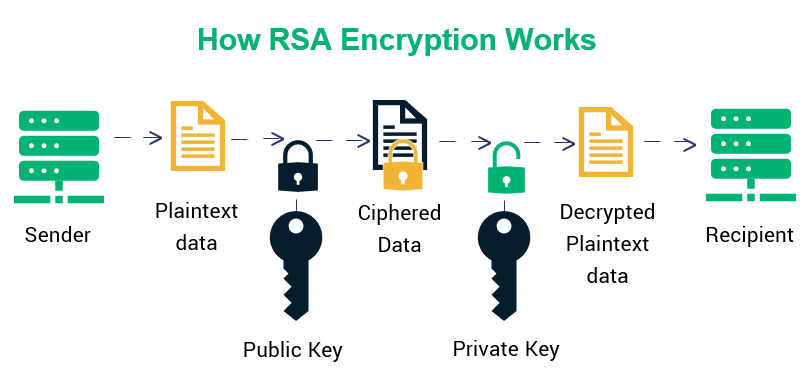
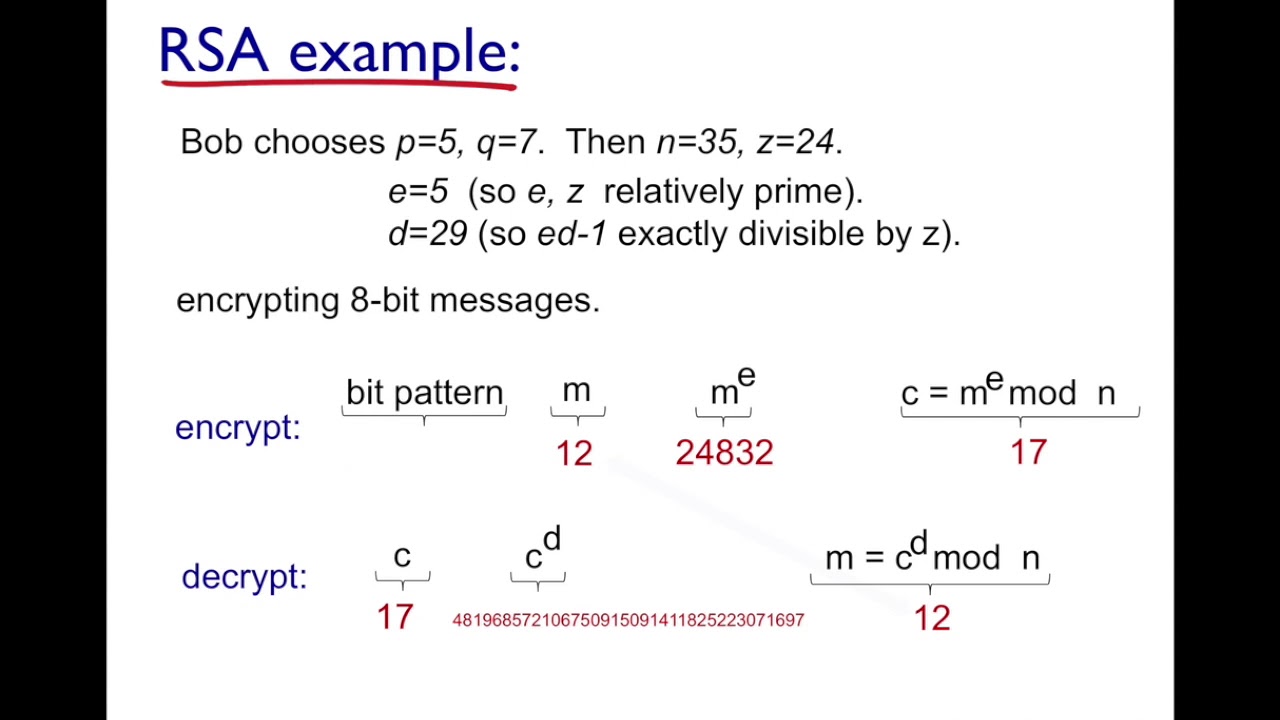
RSA Encryption Unveiled: A Simplified Guide with a Toy Mathematical Example | by Abhisheyk Gaur | Medium
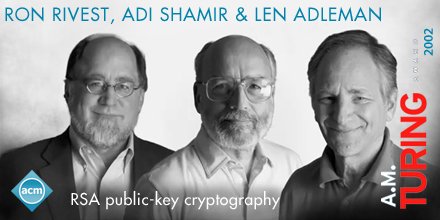
Association for Computing Machinery on X: "Len Adleman, Ron Rivest, and Adi Shamir developed the “RSA method,” now #PublicKeyCryptography. #TuringAward https://t.co/GsnWTWT5iM" / X






![PDF] 2 . 2 RSA ( Rivest Shamir Adleman ) | Semantic Scholar PDF] 2 . 2 RSA ( Rivest Shamir Adleman ) | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/8537133b6738aee132926a6986ce73fe5f2b4ebb/3-Figure2-1.png)




![PDF] 2 . 2 RSA ( Rivest Shamir Adleman ) | Semantic Scholar PDF] 2 . 2 RSA ( Rivest Shamir Adleman ) | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/8537133b6738aee132926a6986ce73fe5f2b4ebb/1-Figure1-1.png)